20. Topic 3, Contoso, Ltd. (NEW)
Case Study
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. When you are ready to answer a question, click the Question button to return to the question.
Overview
Contoso, Ltd. is a consulting company that has a main office in Montreal and branch offices in Seattle and New York.
Contoso has a Microsoft 365 E5 subscription.
Network Environment
The network contains an on-premises Active domain named Contoso.com.
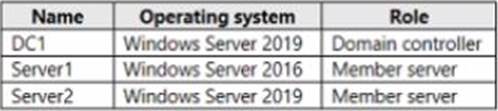
The domain contains the servers shown in the following table.
Contoso has a hybrid Azure Active Directory (Azure AD) tenant named Contoso.com.
Contoso has a Microsoft Store for Business instance.
Users and Groups
The Contoso.com tenant contains the users shown in the following table.
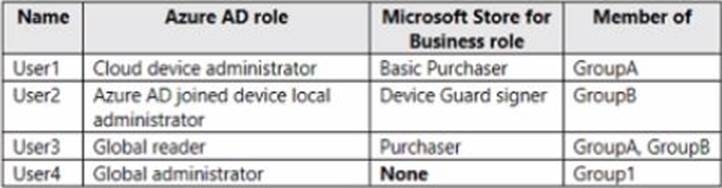
All users are assigned a Microsoft Office 365 license and an Enterprise Mobility + Security E3 license.
Enterprise State Roaming is enabled for Group1 and GroupA.
Group and Group have a Membership type of Assign
Devices
Contoso has the Windows 10 devices shown in the following table.
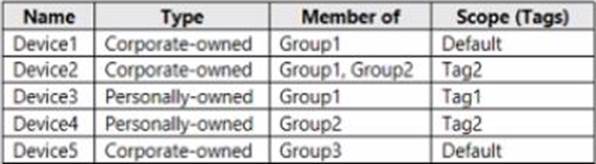
The Windows 10 devices are joined to Azure AD and enrolled in Microsoft intune.
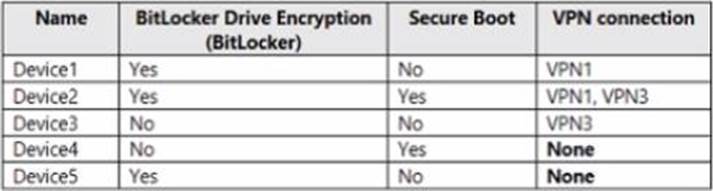
The Windows 10 devices are configured as shown in the following table.
All the Azure AD joined devices have an executable file named C:AppA.exe and a folder named D:Folder 1.
Microsoft Endpoint Manager Configuration
Microsoft Endpoint Manager has the compliance policies shown in the following table.
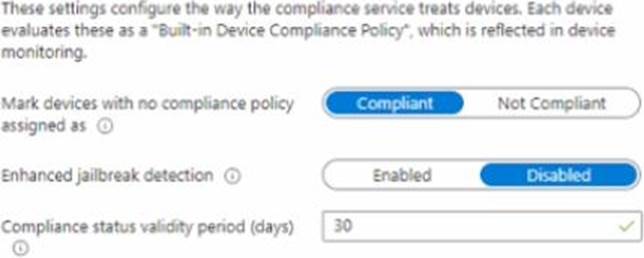
The Compliance policy settings are shown in the following exhibit.
The Automatic Enrolment settings have the following configurations:
• MDM user scope GroupA
• MAM user scope: GroupB
You have an Endpoint protection configuration profile that has the following Controlled folder access settings:
• Name: Protection1
• Folder protection: Enable
• List of apps that have access to protected folders: CVAppA.exe
• List of additional folders that need to be protected: D:Folderi1
• Assignments
Windows Autopilot Configuration
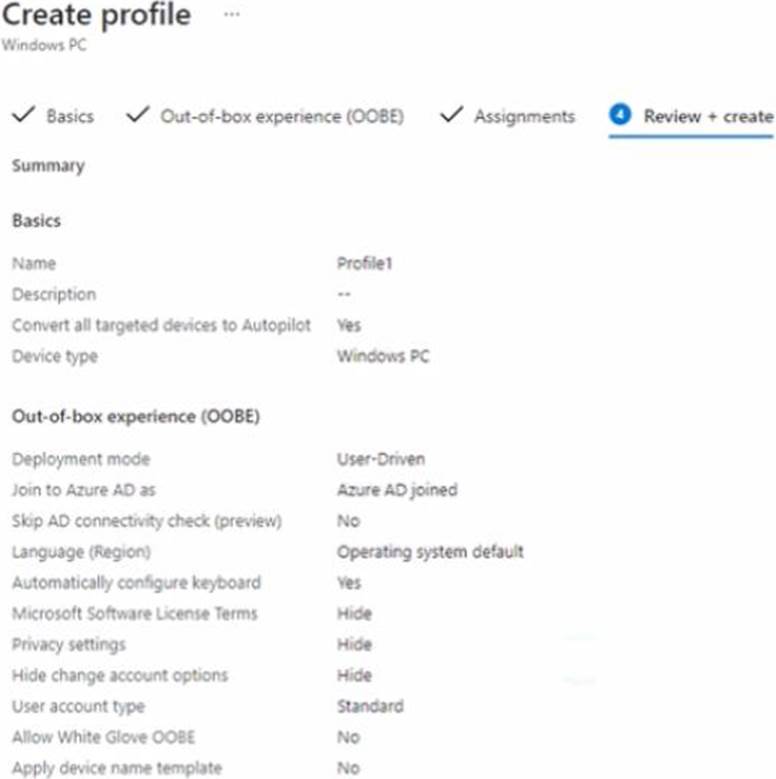
Currently, there are no devices deployed by using Window Autopilot
The Intune connector tor Active Directory is installed on Server 1.
Planned Changes
Contoso plans to implement the following changes:
• Purchase a new Windows 10 device named Device6 and enroll the device in Intune.
• New computers will be deployed by using Windows Autopilot and will be hybrid Azure AO joined.
• Deploy a network boundary configuration profile that will have the following settings:
• Name Boundary 1
• Network boundary 192.168.1.0/24
• Scope tags: Tag 1
• Assignments;
• included groups: Group 1. Group2
• Deploy two VPN configuration profiles named Connection! and Connection that will have the following settings:
• Name: Connection 1
• Connection name: VPNI
• Connection type: L2TP
• Assignments:
• Included groups: Group1. Group2, GroupA
• Excluded groups: ―
• Name: Connection
• Connection name: VPN2
• Connection type: IKEv2 i Assignments:
• included groups: GroupA
• Excluded groups: GroupB
• Purchase an app named App1 that is available in Microsoft Store for Business and to assign the app to all the users.
Technical Requirements
Contoso must meet the following technical requirements:
• Users in GroupA must be able to deploy new computers.
• Administrative effort must be minimized.
You implement Boundary1 based on the planned changes.
Which devices have a network boundary of 192.168.1.0/24 applied?

Leave a Reply